Advanced Networking and the Blind Spot in Modern Security


The Risk Most Teams Assume Is Covered
Over the last decade, enterprises have made substantial investments in identity, endpoint protection, and zero-trust access controls. Data at rest is encrypted. Privileged access is governed. Audit trails are captured. And yet one layer remains structurally under-addressed: data in motion is routinely assumed to be protected simply because it is encrypted. That assumption is wrong. Encryption protects payloads. It does not protect paths.
In distributed environments where workloads span cloud regions, third-party providers, and hybrid infrastructure, transport itself is part of the security boundary. A transport layer that is predictable, observable, or dependent on static tunnels introduces risk that identity controls and endpoint hardening simply cannot reach.
For organizations running regulated workloads inside Tehama Enclaves, this is not a theoretical concern. Enclaves frequently become mission-critical environments. When connectivity fails, work stops. When traffic can be observed or disrupted, compliance exposure and operational risk arrive simultaneously.
The security conversation has to expand beyond access control. Resilience at the transport layer belongs in the same discussion.
Why Traditional Connectivity Models Fall Short
VPNs and SD-WAN architectures were designed for a more centralized world, one that assumed stable perimeters and predictable traffic flows between known sites. In practice, most VPN deployments rely on static tunnels with exposed endpoints; once established, those tunnels stay visible. Traffic patterns can be observed over time, and communication paths remain consistent enough to map.
That visibility creates opportunity for whoever is watching.
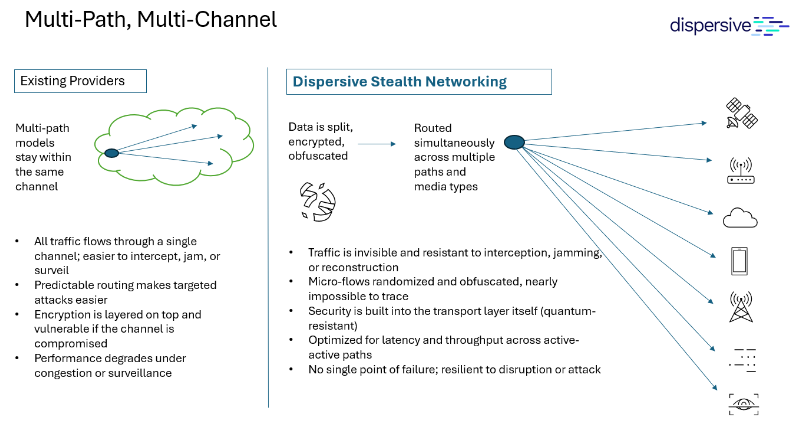
Diagram 1: Traditional VPN vs Dispersive® Stealth Networking
Denial-of-service attacks target exposed gateways. Infrastructure disruption can isolate a single communication path entirely. And even when payloads are encrypted, traffic analysis reveals meaningful patterns about who is communicating, with whom, and how often.
In high-value environments, adversaries don’t always pursue immediate breach. Sustained observation and strategic disruption can accomplish the same objective, on a longer timeline.
For businesses running regulated workloads inside secure enclaves, connectivity is not a convenience layer – it is operational infrastructure. A transport model that introduces single points of failure, or one whose patterns are observable over time, is a business continuity concern.
The Expanding Risk to Data in Motion
Modern attack strategies increasingly focus on the transport layer. Volumetric disruption, path targeting, and traffic interception are no longer sophisticated capabilities reserved for nation-state actors. They are routine. For organizations handling Controlled Unclassified Information, financial data, or healthcare workloads, disruption is not merely an IT event. It can trigger both compliance exposure and operational shutdown simultaneously.
A growing concern is the rise of Harvest Now, Decrypt Later strategies. In these scenarios, adversaries collect encrypted traffic today, expecting that future advances in cryptography or computing will enable decryption later. The immediate objective is not access but accumulation. Long-lived secrets, static communication paths, and predictable endpoints are not just security risks – they are long-term intelligence assets for a patient adversary.
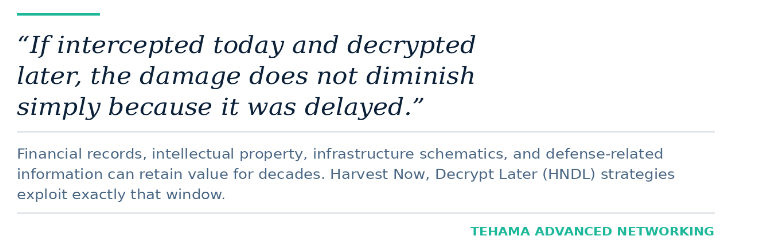
The answer to why this matters today lies in how long regulated data retains its value. Infrastructure schematics, defense-related information, financial records, and intellectual property do not become less sensitive over time. If intercepted now and decrypted later, the damage is not diminished because it was delayed. Reducing what can be captured in the first place matters as much as strengthening the encryption that protects it.
Resilience Is Not Just Encryption Strength
Encryption strength and resilience are not the same thing, though the distinction gets blurred in most security conversations. You can deploy the strongest cipher suite available and still lose connectivity under pressure. You can rotate keys aggressively and still depend on a single exposed gateway that a volumetric attack can take offline. Neither choice protects availability.
In real environments, outages rarely look elegant. A gateway gets saturated, a routing dependency fails or a cloud region drops. What matters in those moments is whether communication can reroute and continue operating, not whether the underlying algorithm was mathematically sound. Resilience at the transport layer means the system does not depend on a single predictable path. Traffic shifts, channels fragment, and flows redistribute without manual intervention. If part of the network is degraded or deliberately targeted, the rest continues operating.
For organizations running regulated workloads inside Tehama Enclaves, this becomes operational, not theoretical. When enclaves support contractor access, compliance reporting, or revenue-generating systems, downtime is not an inconvenience. It is exposure. An attacker does not need to breach the enclave to cause harm. Taking it offline is often enough.
Resilient transport reduces that leverage. It eliminates the single choke point, makes denial-of-service a far less effective tactic, and ensures the infrastructure underpinning secure work remains available when it matters most.
Real-World Example: When Architecture Determines the Outcome
The value of resilient network architecture is clearest during disruption.
During last year’s CrowdStrike update incident, many organizations experienced outages or lost access to critical systems. Some continued operating without interruption, not by luck, but because their environments were built to contain failure.
In one case, a major low-earth satellite provider had deployed Tehama Advanced Networking to support administrative access while keeping operational workloads isolated. The environment followed an N+1 design with strict site separation between sensitive systems and general IT infrastructure. When the faulty update propagated, that separation held. The zero-trust boundary blocked compromised content from reaching protected environments, and both administrative access and operational systems continued running throughout.
Resilience was built into the architecture. What disrupted others was contained.
Moving Beyond Perimeter Thinking
Many organizations still treat networking as a fixed substrate beneath security controls. That assumption no longer reflects reality. In distributed environments, transport must be governed with the same rigor as identity and workload isolation. Connectivity should be policy-driven, aligned with workload context, and continuously evaluated. Zero trust cannot stop at the access layer; the transport layer must also assume untrusted conditions.
This shift requires a different architectural mindset: design for adaptability rather than hardening a central gateway, implement dynamic routing rather than relying on static tunnels, and reduce endpoint visibility rather than assuming exposure is manageable.
When transport is treated as part of the security boundary, availability and confidentiality reinforce each other.
Governance and Availability Must Coexist
In regulated environments, governance requirements extend beyond access logs.
Organizations must demonstrate that secure transmission controls are operating as designed, that connectivity policies are consistently enforced, and that communication paths align with their compliance obligations. Traditional monitoring approaches often introduce additional exposure by creating inspection points that themselves become targets. A modern transport architecture must balance observability with confidentiality. It should allow policy enforcement and auditability without exposing payloads or creating static choke points.
When implemented correctly, transport resilience becomes auditable rather than opaque.
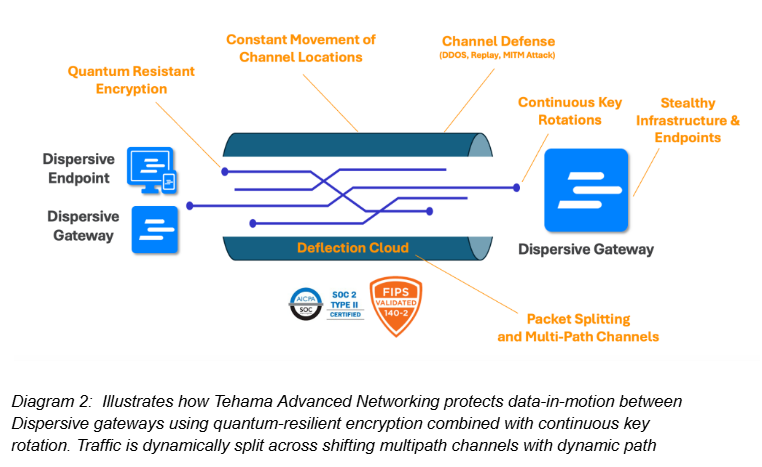
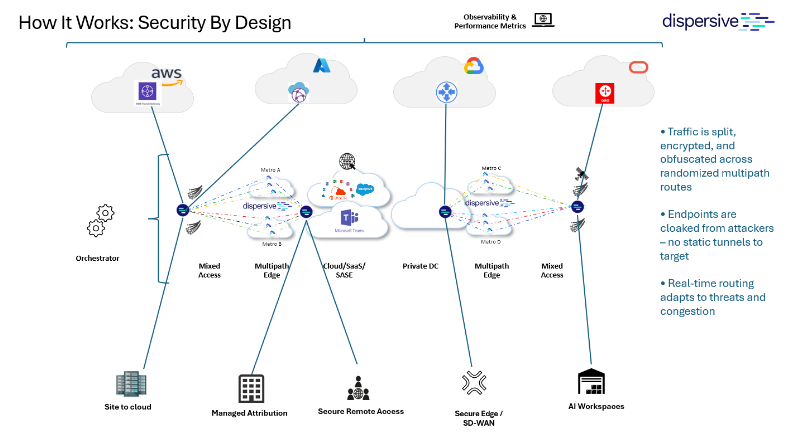 Diagram 3: Transport-layer enforcement assumes a networking layer capable of dynamic, non-observable path control. Underlying transport enforcement powered by Dispersive® Stealth Networking
Diagram 3: Transport-layer enforcement assumes a networking layer capable of dynamic, non-observable path control. Underlying transport enforcement powered by Dispersive® Stealth Networking
Quantum Resilience and Architectural Durability
The threat landscape is not static. Nation-state actors are already stockpiling encrypted traffic in anticipation of future cryptographic advances.
Quantum resilience is not a marketing term. It reflects a real architectural choice: systems built around long-lived secrets and fixed tunnels are difficult to evolve as cryptographic assumptions change, while architectures designed around dynamic paths, fragmentation, and cryptographic agility are not.
From a transport perspective, quantum resilience reduces the value of intercepted traffic and limits long-term exposure. It acknowledges that cryptographic assumptions may change, and it avoids building permanent dependencies into the communication fabric.
The objective isn’t to predict the exact timeline of quantum breakthroughs. It is to ensure that today’s design choices do not create tomorrow’s liabilities.
How Tehama Advanced Networking Protects Mission-Critical Enclaves
Tehama Advanced Networking extends enclave-level governance into the transport layer. Powered by Dispersive® Stealth Networking, it fragments, encrypts, and distributes traffic across dynamically shifting paths. There are no static tunnels to target, no exposed gateways to overwhelm, and no predictable communication patterns to observe over time.
For organizations that rely on Tehama Enclaves to operate regulated, compliance-bound workloads, this matters operationally. If an adversary attempts volumetric disruption or path targeting, the architecture is designed to maintain availability. An adversary cannot simply take your enclave offline by overwhelming a single endpoint.
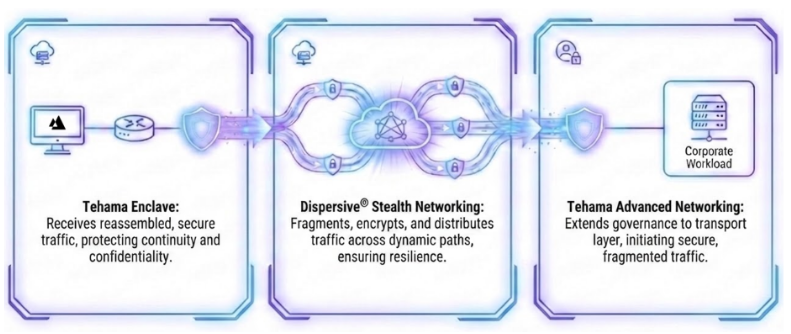 Diagram 4: Tehama secure connectivity architecture showing how traffic is initiated and governed from the Tehama enclave, fragmented and encrypted across dynamic paths by Advanced Networking by Dispersive Stealth Networking, and reassembled for sensitive workload access
Diagram 4: Tehama secure connectivity architecture showing how traffic is initiated and governed from the Tehama enclave, fragmented and encrypted across dynamic paths by Advanced Networking by Dispersive Stealth Networking, and reassembled for sensitive workload access
Advanced Networking protects confidentiality, but it also protects continuity. In environments where secure access underpins revenue, regulatory posture, and partner trust, resilience at the transport layer becomes a strategic requirement.
Data-in-motion protection is no longer an accessory control. It is core infrastructure.

Read More

Driving Better Business Outcomes with SASE

HIPAA Compliance Doesn’t Have to Be Complicated: Meet Tehama for Healthcare


